Professionals across the industry's largest banks, asset managers, hedge funds, and fintechs rely on interop.io every day and have realized the benefits of streamlined workflows. Contact us to learn how we can jump start your interoperability project.
Welcome to interop.io, where we bring together two world-renowned interoperability platforms (Glue42 and Finsemble) to deliver the best in application integration, user experience, and smart, automated workflows. With interop.io, clients build customized solutions to help users focus on higher-value tasks and experience a new, streamlined way to work.
Making your work flow
By syncing, linking, and connecting any type of application, interop.io allows you to streamline the rote tasks of your traders, PMs, compliance officers, and back office personnel, freeing them to focus on higher value tasks. Connect your OMS, market data terminal, inventory management system, and CRM, so that multi-step processes are streamlined. Benefits include:
- Respond to client requests faster
- Deliver contextual insight and trade ideas to clients during calls/chats
- Improve the efficiency and effectiveness of the trading desk
- Deliver a better client experience
From expediting sales and trading processes to streamlining communications across groups, interop.io is here to help.
Let’s build workflows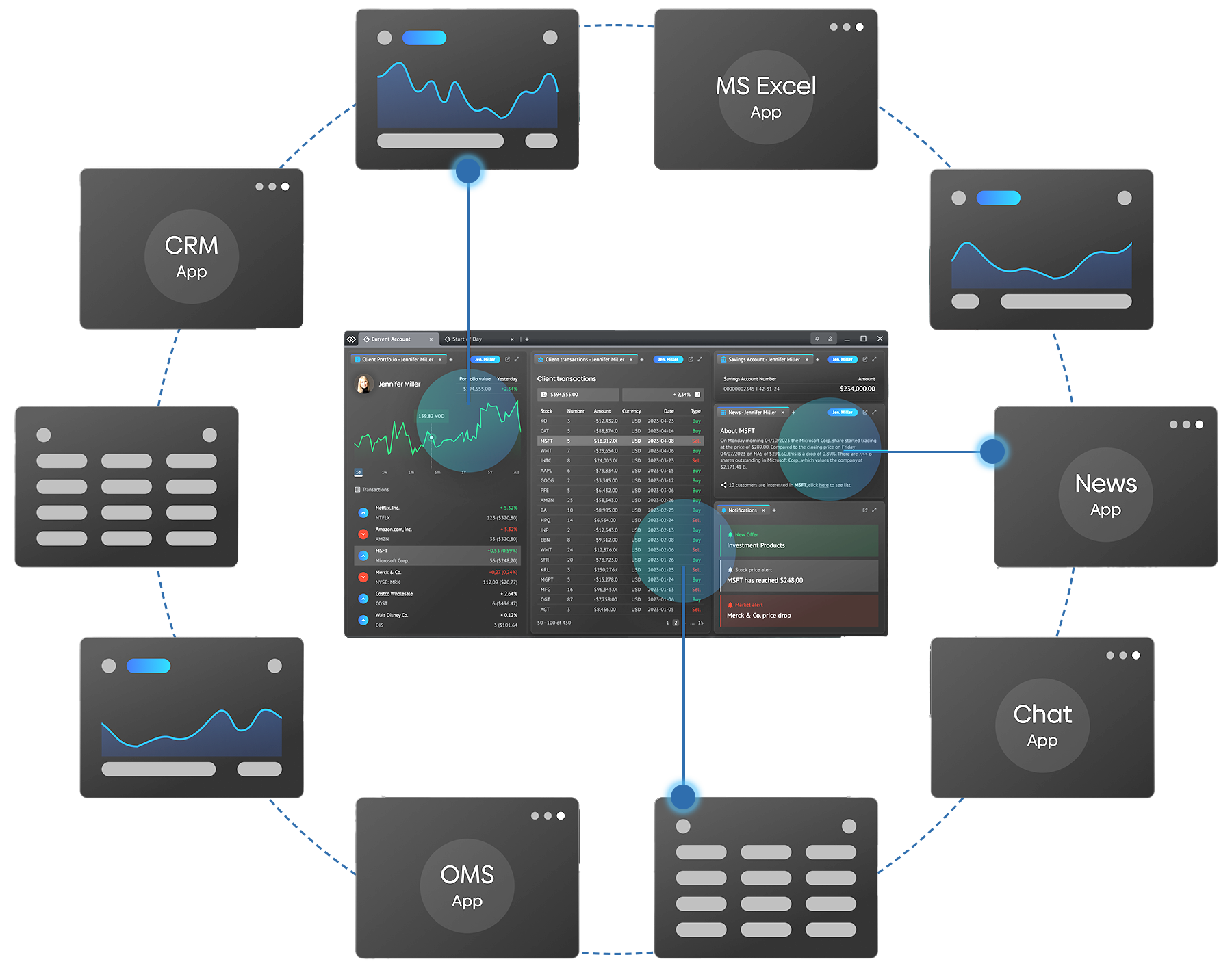
The trusted partner
for your interoperability project
Across capital markets the business case for interoperability is clear. Too many siloed applications and legacy technologies have led to application overload and fragmented, inefficient workflows. interop.io is the trusted partner you need for a successful interoperability project in record time to market with demonstrable return on investment.
Industry award-winning implementations
Connect anything to everything
By bringing together the best in tech from the Glue42 and Finsemble product lines, we’ve expanded the roster of available technologies to be included in your workspace. You won’t find support for native, virtual (such as Citrix), and legacy in-house apps anywhere else, along with out-of-the-box connectors for Bloomberg, Fidessa, Salesforce, Excel, and many more. Learn more about io.Connect adapters.
FDC3 — The heart of interoperability
FDC3 is a lightweight, industry standard for desktop interoperability—but it doesn’t specify everything. It is a jumping off point to build a cohesive desktop environment with interconnected applications. interop.io’s FDC3-certified desktop agent provides additional workflow capabilities to meet your real-world use cases.